How to Modernize Physical Security
- GK Tieo
- Apr 15
- 6 min read
A badge printer jams at 7:30 a.m., a delivery driver is waiting at the dock, and the only person who can approve access is across town. That is usually when teams stop asking whether legacy security is inconvenient and start asking how to modernize physical security in a way that actually reduces risk.
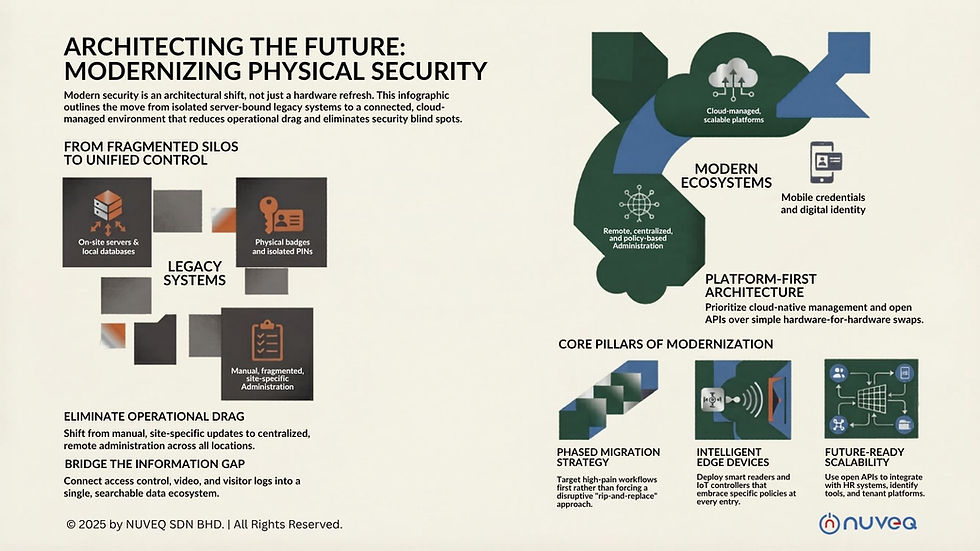
For most organizations, modernization is not about replacing every door controller overnight. It is about moving from isolated hardware and manual processes to a connected security environment that can be managed centrally, scaled across sites, and adapted as threats and operations change. The strongest programs do not just add newer devices. They remove friction, improve visibility, and give security and operations teams better control without adding more infrastructure to maintain.
Why physical security modernization matters now
Legacy systems tend to fail in familiar ways. They rely on on-site servers, local databases, and fragmented tools that do not communicate well with each other. One building uses keycards, another uses PINs, a third has a standalone visitor log, and video is managed somewhere else entirely. That setup creates blind spots.
The problem is not only security exposure. It is also operational drag. Every manual credential update, every on-site reboot, and every disconnected report consumes time that security, IT, and facilities teams do not have. As organizations expand locations, support hybrid work, and face stricter compliance expectations, older systems become harder to justify.
Modernization changes the operating model. Instead of managing access, visitors, identities, and events through separate tools, teams can move toward a unified platform with remote administration, live visibility, and policy-based control. That is where the business value starts to show up.
How to modernize physical security without creating new complexity
A common mistake is treating modernization as a hardware refresh project. In practice, the first step is architectural. You need to decide whether your future system will still depend on local infrastructure and siloed products, or whether it will be built around cloud-native management and open integration.
That distinction matters. Swapping old readers for newer readers may improve reliability at the edge, but it will not solve fragmented administration or limited reporting. A modern approach starts with the platform, then layers in devices and integrations that fit your workflows.
Start with your operating pain points
Before selecting technology, identify where your current environment breaks down. For some organizations, the biggest issue is decentralized administration across multiple sites. For others, it is poor identity verification, inconsistent visitor handling, or the cost of maintaining on-premise servers. In regulated settings, audit gaps may be the main driver.
Those priorities should shape the roadmap. A corporate office and a logistics campus may both want stronger access control, but the right mix of mobile credentials, vehicle access, biometrics, or video integration will differ. Modernization works best when it is tied to real use cases instead of broad claims about being more advanced.
Replace isolated systems with a connected ecosystem
The biggest leap comes from unifying systems that were previously managed in isolation. Access control should not sit apart from visitor management, identity verification, license plate recognition, elevators, gates, turnstiles, and video. When these systems share data and context, the security team can make better decisions faster.
For example, a visitor pre-registration workflow can trigger temporary access rights, notify hosts, and log entry events automatically. A denied credential event can be cross-checked against video and identity data without jumping between systems. Vehicle access can be managed as part of the same policy framework as door access. That is more than convenience. It reduces delays, manual errors, and opportunities for misuse.
Move administration to the cloud
If you are serious about how to modernize physical security, cloud architecture should be part of the discussion early. Cloud-managed systems reduce dependence on local servers, simplify software updates, and give administrators the ability to manage sites remotely from a single interface.
This matters most in distributed environments. A property group with multiple buildings, a healthcare network, or a school system cannot scale efficiently if every location needs hands-on server maintenance and separate administrative workflows. Centralized cloud management gives teams a common view across facilities while still allowing site-specific policies where needed.
There are trade-offs, and they should be evaluated carefully. Some organizations need to review data residency, network resilience, and integration requirements before moving core security functions to the cloud. But for many enterprises, the gains in scalability, uptime management, and administrative efficiency outweigh the old server-based model.
The technologies that make modernization real
Technology choices should support a stronger operating model, not distract from it. The goal is to create a system that is more responsive, easier to manage, and better aligned with how people actually move through a facility.
Mobile credentials and digital identity
Plastic badges still have a place, but they are no longer the only practical standard. Mobile credentials reduce printing, replacement, and handoff delays while giving administrators more control over issuance and revocation. They also fit better with temporary users, contractors, and hybrid staff who do not need permanent cards.
Digital identity verification adds another layer. Instead of relying only on what someone presents at the door, organizations can verify who they are earlier in the workflow. That is especially useful in workplaces with onboarding requirements, residential properties managing guests, and sites with sensitive areas where identity assurance matters as much as entry permission.
Smarter edge devices
Modern readers, biometric devices, IoT controllers, and intelligent barriers can extend policy enforcement beyond the front door. The benefit is not just stronger authentication. It is better orchestration of physical movement across a site.
Still, not every opening needs the highest level of control. A data center cage, an executive suite, and a common office entrance have different risk profiles. Modernization should reflect that. Overengineering every entry point raises costs without always improving outcomes.
Video and event correlation
Video becomes more valuable when it is part of the access conversation rather than a separate archive. When events can be correlated across entry logs, alarms, and footage, investigations become faster and more accurate. Security teams spend less time stitching together timelines and more time responding.
This is particularly effective in environments with high visitor volume, vehicle traffic, or compliance reporting needs. Connected video services can also reduce infrastructure burdens compared with older recorder-heavy deployments, although bandwidth planning and retention requirements still need close attention.
Build for scale, not just for the next site
Many organizations modernize after outgrowing a single facility. The trap is deploying a system that solves the immediate location problem but creates the same fragmentation again at a larger scale.
A future-ready design supports centralized administration across thousands of doors, multiple user groups, and changing facility needs. It also allows phased deployment. You may begin with access control and visitor management, then add biometrics, elevator controls, ANPR, or broader automation later. Open APIs are important here because they protect flexibility. They give organizations room to integrate with HR systems, tenant platforms, identity tools, and other operational software without getting boxed into a dead end.
This is where a solution-driven provider can make a measurable difference. A company like NUVEQ approaches modernization as an ecosystem decision, combining cloud-native access control, connected devices, and integrations into one enterprise-ready framework. That model is often more effective than buying separate parts and hoping they work together cleanly afterward.

How to modernize physical security with less disruption
The best modernization projects do not force a dramatic cutover unless there is a compelling reason. In many facilities, a phased approach is smarter. Start with the sites or workflows causing the most operational pain, then expand once the model is proven.
That might mean migrating remote administration first, standardizing credential policies next, and integrating visitor management after that. For other organizations, the first win may be replacing server-dependent architecture with a cloud-managed platform while preserving selected hardware during transition. It depends on asset condition, compliance needs, and budget timing.
What matters is governance. Define who owns access policy, who approves identity workflows, how incidents are reviewed, and what data needs to be retained. Modern systems make better control possible, but they do not replace the need for clear operational rules.
A modern physical security strategy should feel lighter to manage, not heavier. If the new environment still requires too many manual workarounds, too much local maintenance, or too much jumping between systems, it is not really modernized. The real benchmark is whether your team can see more, control more, and respond faster with less infrastructure standing in the way.
The smartest next step is usually not a full rip-and-replace. It is choosing an architecture that can carry your security program forward for years without forcing you to rebuild it every time your business grows.








Comments